Search
Roles and responsibilities
Although the ID authority has primary accountability for the implementation of the ID system, their role throughout the identity lifecycle may be lean or robust. Beyond setting overall standards and policies and engaging with the public, the ID authority may also fill one or more of the following roles throughout the identity lifecycle: (1) collecting and proofing identity data, (2) managing identities and data, (3) issuing, replacing, and revoking credentials, and (4) providing identity authentication and verification services (see Figure 16).
Figure 16. Example institutional roles within an ID system
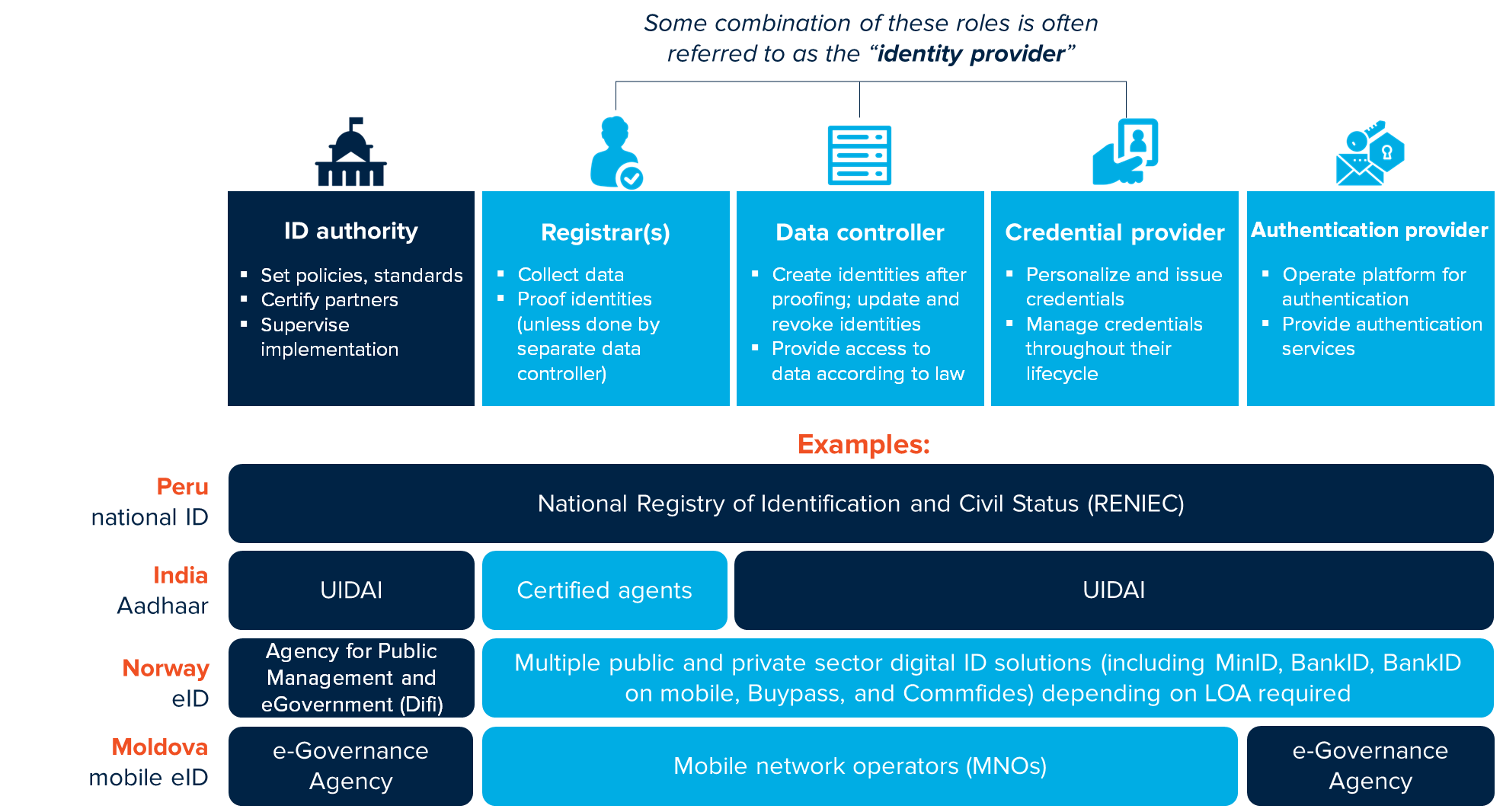
Source: Adapted from the Digital Identity Toolkit, with information on Norway from http://eid.difi.no/en/how-register-new-user-id-porten.
The division of roles has important implications for the overall functioning of the ID system as well as costs and data protection and privacy. In some cases—e.g., Peru—the ID authority fulfills all of these roles. In other cases, these roles may be assigned or adopted by different agencies, implemented in partnership with the private sector, or outsourced entirely. Vertical integration of ID-related activities has some benefits, including clear lines of authority and accountability for the ID system. At the same time, partnerships and/or the outsourcing of some functions may allow the ID authority to lower its initial investment costs and keep a relatively smaller footprint. This has been the route taken for some countries—e.g., the UK, Sweden, Norway, Denmark, and Moldova—creating digital authentication layers and services to facilitate log-in for e-services.
From a privacy perspective, it may also be advantageous to divide the responsibilities of the ID system between multiple actors, such as separating the roles of authentication provider and authorization provider from identity provision. This “separation of duties” limits the power of any single entity, potentially reducing the risk associated with a single “rogue” administrator or agency. In addition to separating roles within the identity lifecycle, it implementing the principle of “least privilege”—which ensures that any administrator only has the powers necessary to perform their delegated function, and no more—will also help protect personal data from misuse (see the IDEEA framework for more).
Another argument for devolving the authentication services is that it may encourage innovation. Levels of assurance and the nature of the service will differ by use case, and providers of authentication services may be able to offer the appropriate technology better than a centralized agency. They may also be in a better position to make the requisite infrastructural investments than a government entity (e.g., the banking sector).
Figure 17. Key considerations for roles and responsibilities
 |
 |
 |
 |
|---|---|---|---|
| Reliability | Data Protection | Sustainability | Responsiveness |
| All entities involved in the ID lifecycle must be capable and trusted to manage core processes. | Separation of duties across agencies may help limit power and provide checks and balances for the ID system. | Well-implemented partnerships may reduce upfront costs and footprint of the ID authority. | Lines of accountability may be clearer in cases where the ID authority plays a central and transparent role in identity provision. |
